
Encryption in general
Psono didn’t reinvent the wheel. In Psono’s core, we are using Curve25519 and Salsa20 in form of NaCl (pronounced “salt”) the “Networking and Cryptography library”. Our server uses PyNaCl and our frontend ecma-nacl. Both are well established implementations of NaCl. Why not RSA and AES? RSA and AES are far more famous but are easy to implement wrong and far slower (here is a useful article that talks about differences and the “dangers” of using RSA and AES).
Your Browser Encryption
Psono encrypts all data (like passwords, or notes) with NaCl’s secret key authentication before leaving your browser and being stored on the server in a “secret object”. The key for the encryption is generated randomly and stored together with some metadata of your secret in your “datastore”. The browser application encrypts your “datastore” with a derivation of your password. As algorithm for this password derivation we are using scrypt. Why not PBKDF2? PBKDF2 is far more famous but due to the lower resource demand (especially memory) “cheaply” implementable in hardware and easier to crack for an attacker.

Our Transport Encryption
Three encryption layers protect your data on its way from your browser to our application server. The base layer is the encryption of the data itself done by the client. On top of that Psono has implemented a mid layer, which we usually refer to as Psono’s transport encryption layer. This layer is like a tunnel (similar to a VPN tunnel) between the website (or extension) running inside your browser and our application server. In addition, on top as outer layer or shell layer we are using HTTPS (in version TLS 1.2). Noteworthy is also, that both our mid and outer layer are built and configured to support perfect forward security (PFS).

The Encryption at Rest

Regular Security Updates
You have to keep your software up to date. That is the best advice for any computer system and software. It’s the best protection against malware, viruses and hackers and a fundamental necessity to protect your secrets. Psono has understood this and releases regular updates with the newest security patches and features.
Open Source Principle
Psono’s core is open source and will stay open source. This means: No license fee. No over time increasing subscription costs. No hidden security flaws. Flexibility to move and host everywhere with the partner of your choice. Public auditability and security checks. You can fix a bug yourself if you want at any time.

Service Availability
You need access to your passwords at all time. We understand that. Psono has three approaches to solve this problem. First, we offer everybody our server and clients for on-premise hosting, free of charge and with docker as easy as it gets. On our download page, you can find the corresponding docker images for the Psono Server and Psono Web Client. Second, our easy text file backup function. Third, we are running in the cloud on Amazon’s AWS and Google’s GCP minimizing the risks of datacenter outages, data loss and server problems.

Daily Backups of your data
We backup all data of the Psono.pw Service automatically every night to ensure the maximum possible protection against potential data loss. Access to those backups is only granted to a very limited amount of people.
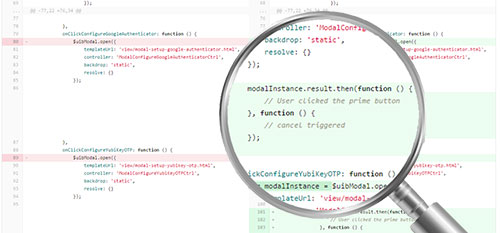
Code safety through Code Audits
We perform code audits on any new code that is added. The code requires manual approval before it’s put into production. Automatic checks ensure the quality of the code.
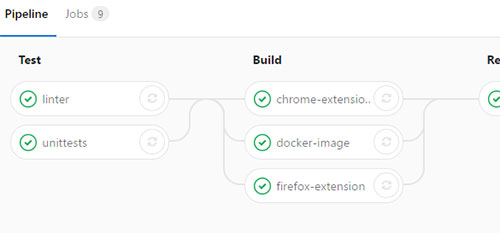
Issue minimization Automated Testing
We test all code automatically on multiple stages and it must pass several quality checks before it's considered to go live. You can find the current status of tests always as a badge here for Psono Client and the Psono Server.

Automated Vulnerability Scans
We have multiple security and vulnerability scanners in place. This allows us to detect new threads and respond quickly. Automated scans run nightly and trigger notifications correspondingly. In addition, those scans are run automatically in our build pipeline, blocking vulnerable releases. Additional checks offered by third parties (e.g. github.com) throw alerts for every new CVE.

Multizone Network Design
Our network is following best practices and uses the full power of security restrictions of our cloud providers. The network itself is split into multiple shells and firewalls in between to restrict access and prevent/delay possible intrusions.

Advanced DDoS Protection
DDoS (Denial-of-Service) attacks are a big threat for current online services. That's why Psono has taken measures to protect itself and uses Cloudflare to mitigate the risk of outages due to DDoS attacks.